TA416 Abused Microsoft's Own OAuth Endpoint to Plant PlugX in EU Missions
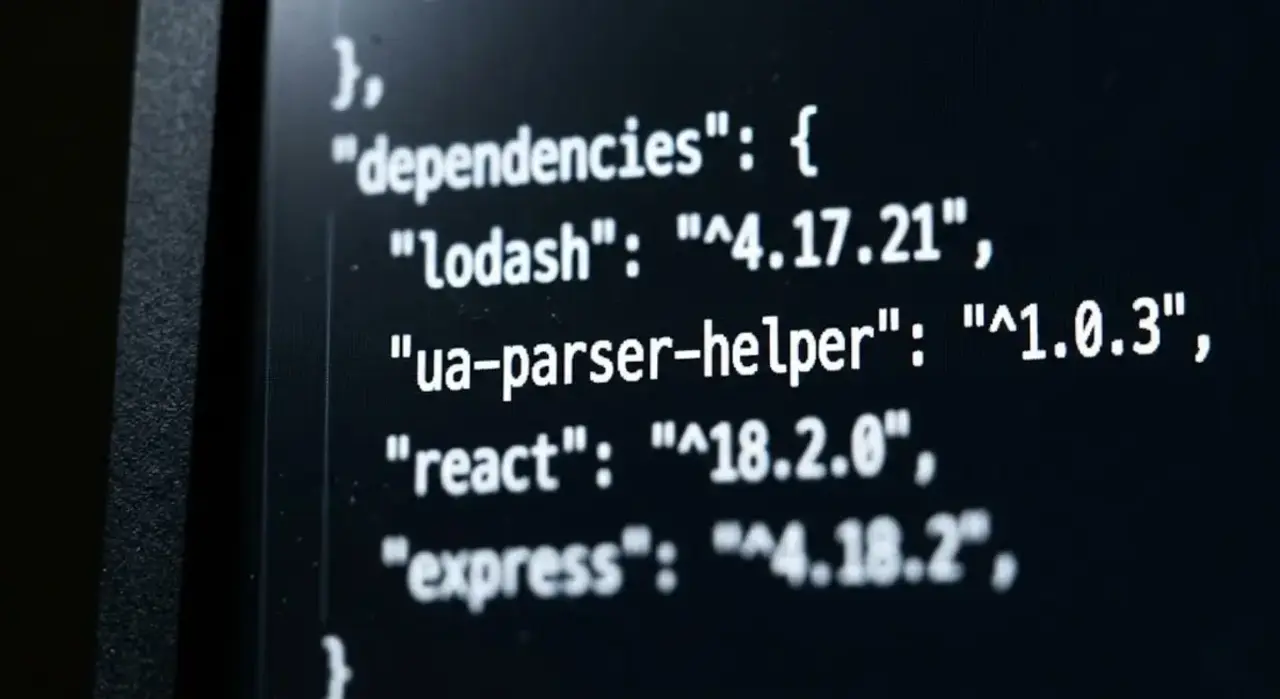
TA416 resumed targeting EU and NATO diplomatic missions in mid-2025 after two years away, using OAuth redirect abuse, Cloudflare Turnstile pages, and MSBuild-based chains to deploy a constantly updated PlugX backdoor. The group's tooling and targeting both shift with geopolitical events.