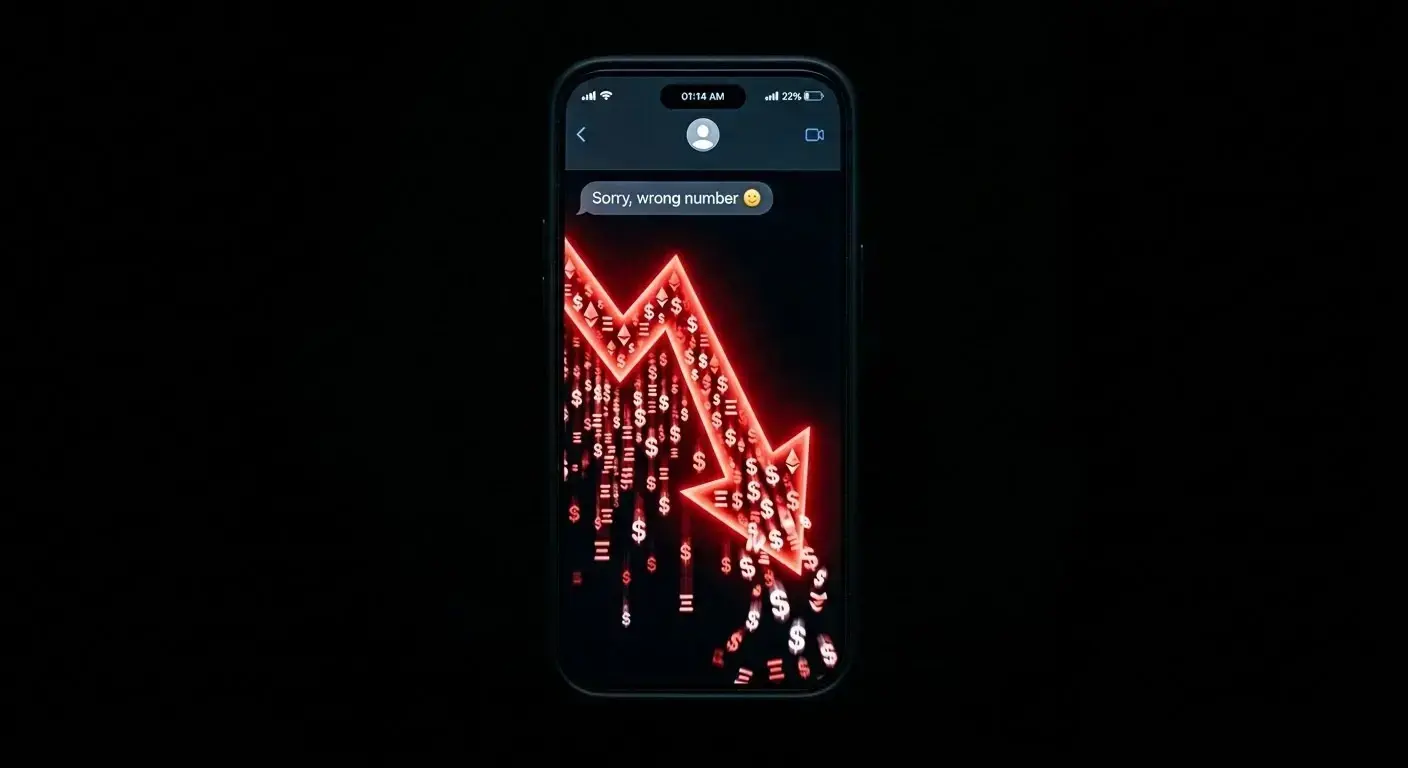
A single text — "Sorry, wrong number" turned into a $3.4 million crypto heist without a single line of malicious code.
Federal prosecutors in Boston have filed a civil forfeiture action to recover roughly $3.44 million in USDt tied to an alleged online investment fraud. Authorities say the funds were seized in early 2025 following an investigation launched in late 2024, after victims across multiple U.S. states reported significant losses.
The case is a clean illustration of where crypto fraud has moved: away from protocol exploits and straight into human psychology.
Victims first received what looked like an accidental message on WhatsApp or Telegram no links, no malware, just a casual "wrong number" opener. From there, scammers played a long game.
Weeks of friendly conversation, personal details shared back and forth, a consistent and reliable persona maintained throughout. By the time any financial topic came up, victims felt like they were talking to someone they knew.
The pitch was deliberate in its construction: an exclusive Ether investment opportunity, supposedly backed by tangible gold holdings. Crypto's growth potential paired with gold's perceived stability — a combination designed to feel both exciting and safe.
Victims were told to buy ETH themselves on legitimate exchanges, then transfer it to wallets the fraudsters controlled. Because victims handled the transaction personally on platforms they recognized, the whole thing felt like genuine investing, not fraud.
It wasn't. Once the ETH arrived, it was routed through a chain of intermediary wallets, converted to USDt, and moved to unhosted addresses. Blockchain records, combined with investigative tools, allowed authorities to trace the money trail and make the seizure. The civil forfeiture proceeding now seeks permanent title to the assets — no criminal conviction required for that process to move forward.
Prosecutors note that no technical vulnerabilities were touched. This operation ran entirely on persuasion. It fits a broader fraud category known as pig-butchering a model in which victims are methodically groomed before being led into financial schemes.
Some of these operations, according to investigators, function like structured businesses: separate teams handle the conversation phase while others manage the crypto transfers.
Red flags that match this pattern:
- Unsolicited messages claiming to be sent by mistake
- Rapid trust-building from someone you've never met
- Conversations that gradually shift toward investment opportunities
- Promises of exclusive access or unusually high returns
- Instructions to send crypto to an external wallet address
If you receive a message like this: do not engage out of politeness, never transfer funds to a wallet address provided by a stranger, and block and report the contact immediately. If funds have already moved, notify law enforcement and the relevant exchange as quickly as possible — speed matters for tracing.
The core vulnerability here was not a protocol flaw. It was the entirely human tendency to be polite to strangers, to trust people we've talked to consistently, and to feel in control when we're the ones pressing the buttons.
⚠️ LEGAL DISCLAIMER: This article is for informational purposes only and does not constitute financial or investment advice.
Source: Cointelegraph