A stolen 2025 Google ad slot just tricked thousands of Mac users into pasting a single malicious Terminal command—and the attackers are watching victim activity in real time.
The ClickFix playbook, once a Windows-only nuisance, has quietly pivoted to macOS under the name MacSync. Three overlapping campaigns since November show how fast the commoditization of infostealers is eroding the last comfortable myth that Apple laptops are too niche to bother with.
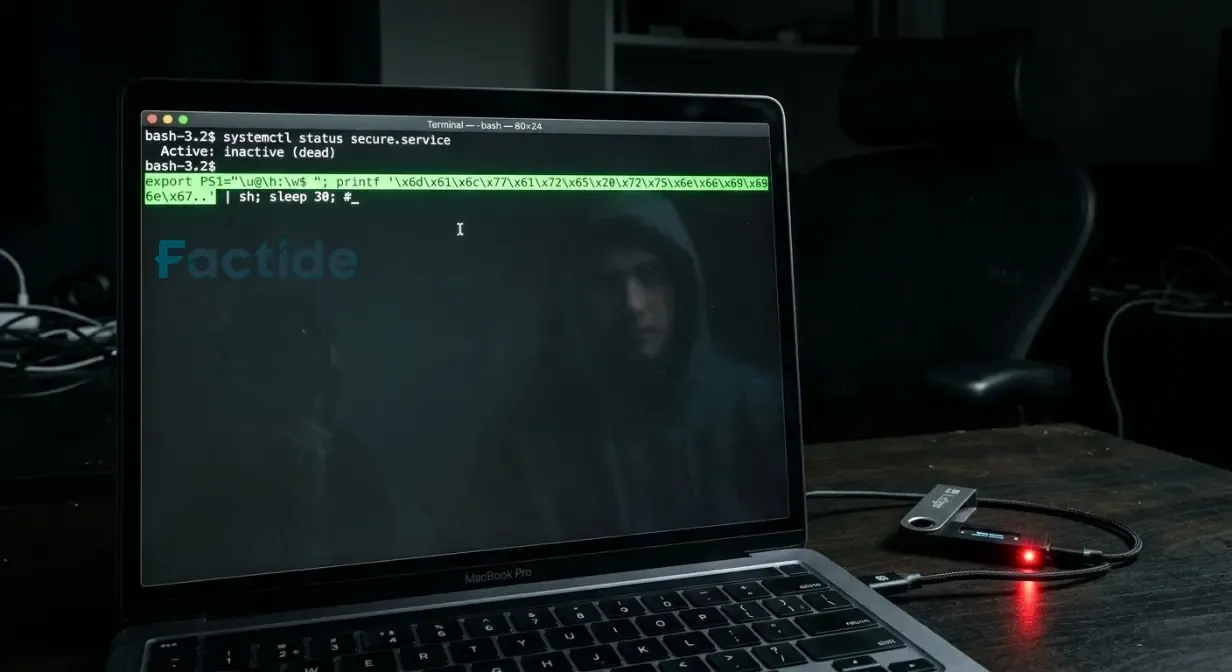
The first wave arrived in November 2025 through a Google-sponsored link that promised an “OpenAI Atlas browser.” The ad pointed to a page hosted on sites.google.com; once clicked, victims were walked through a familiar-looking install flow that ended with a copy-paste command into Terminal. No Gatekeeper alert, no XProtect block.
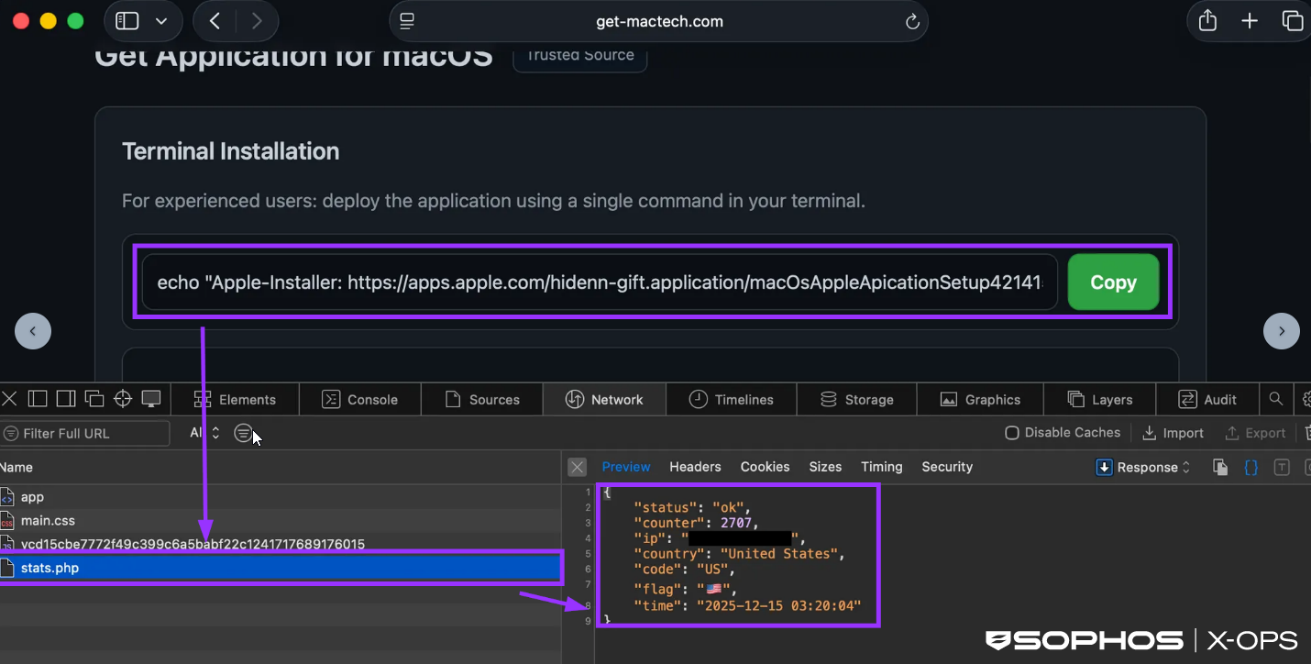
By mid-December the lure had shifted inside shared ChatGPT conversations. A link that appeared to point to GitHub instead served the same payload. The page greeted visitors with a small ego boost: “For experienced users.” Behind the flattery, a stats.php endpoint logged 29,180 clicks by December 18, forwarding each new victim’s IP, user-agent, and timestamp to a Telegram bot in real time.
The February 2026 build adds a multistage loader rented out as a service, an API-gated command-and-control network, and AppleScript that never touches the disk. One of its side hustles is patching the legitimate Ledger Live app: the malware swaps the stock app.asar file for a rigged version that quietly exfiltrates crypto seed phrases the next time the wallet syncs.
Code comments in the loader carry Russian-language markers, but attribution remains murky. What’s clear is that Apple’s notarization pipeline never flagged the re-signed Ledger Live bundle, and the system’s built-in sentinels stayed silent.
Sophos is tracking the family as OSX/InfoStl-FQ, OSX/InfoStl-FR, and OSX/InfoStl-FH. The vendor’s telemetry shows infections across North America and Europe, with no sign the operators are slowing down.
The campaigns don’t bother with zero-days or kernel extensions; they rely on the user’s willingness to paste a “fix” into Terminal. That single gesture disables the only barrier left between the malware and the keychain.
Look, the commoditized infostealer market no longer treats macOS as an afterthought—it’s now a primary target, and the cheapest exploit is still the user who thinks Macs don’t get malware.
Source: Sophos