Two versions of Axios, the JavaScript HTTP client downloaded more than 83 million times a week, were found to contain a malicious dependency after the npm account of the package's primary maintainer was compromised.
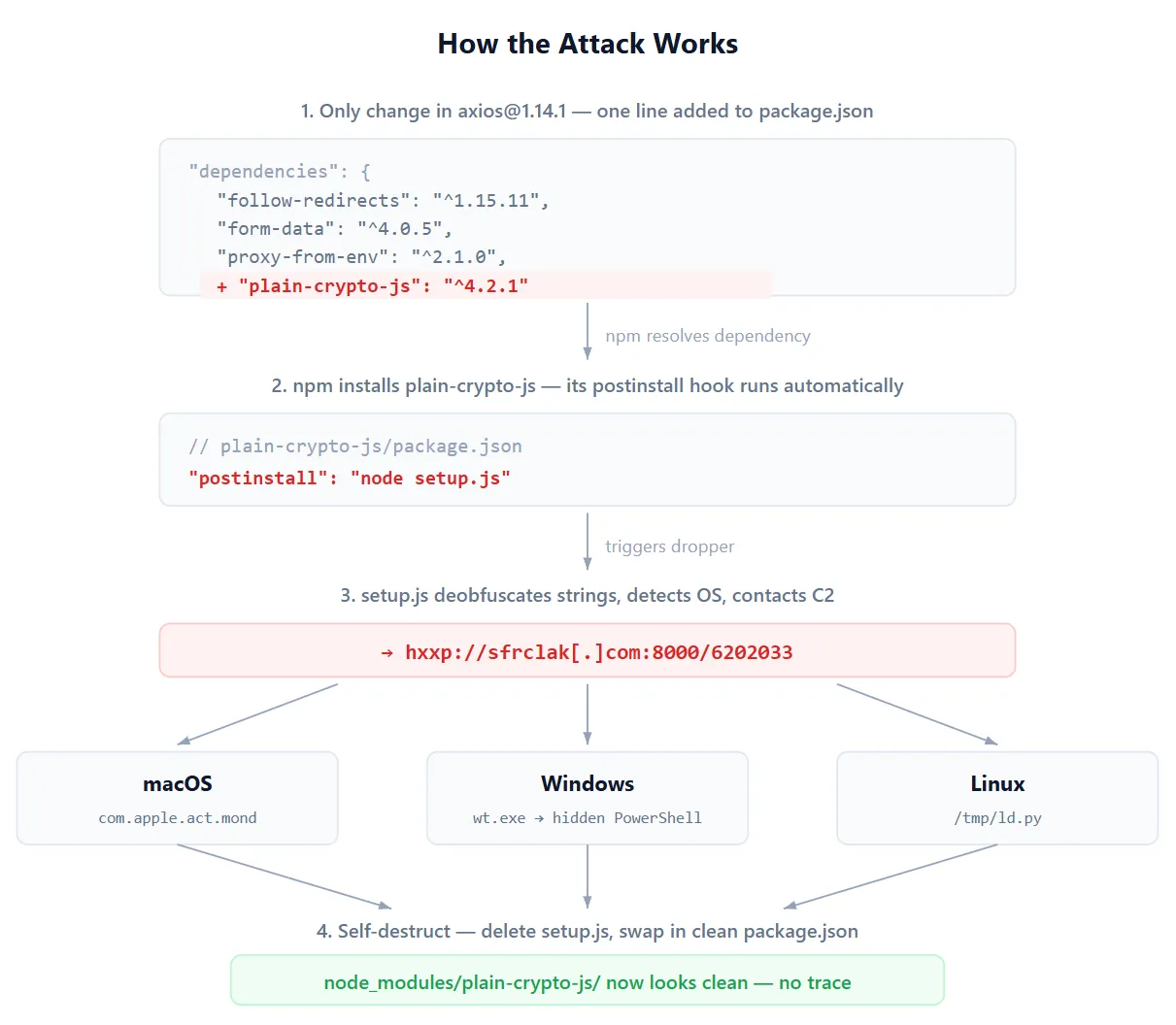
Versions 1.14.1 and 0.30.4, published on March 31, 2026, injected a fake package called plain-crypto-js version 4.2.1 as a runtime dependency. The package does not appear anywhere in Axios's source code. Its only function was to run a postinstall script that deployed a cross-platform remote access trojan.
The attack was not improvised. According to security firm StepSecurity, the malicious dependency was staged 18 hours before the poisoned Axios versions went live. Three separate payloads were pre-built for three operating systems. Both release branches were hit within 39 minutes.
Ashish Kurmi, security researcher at StepSecurity:
"The dropper contacts a live command and control server and delivers platform-specific second-stage payloads. After execution, the malware deletes itself and replaces its own package.json with a clean version to evade forensic detection."
On macOS, the dropper ran an AppleScript payload to fetch a trojan binary from an external server, save it under a path disguised as a system cache file, and launch it in the background before deleting itself. On Windows, it copied the PowerShell binary, disguised it as the Windows Terminal application, and executed a VBScript that fetched and ran a PowerShell RAT. On Linux and other platforms, a shell command fetched a Python RAT script saved to the /tmp directory and ran it using nohup.
The downloaded macOS binary is a C++ RAT that fingerprints the system and contacts a remote server every 60 seconds to receive commands. It can execute shell commands, run additional payloads, enumerate the file system, and terminate itself.
The threat actor had compromised the npm account of "jasonsaayman," the primary Axios maintainer, and changed its registered email to a Proton Mail address. The fake plain-crypto-js package was published by a separate npm user with a different Proton Mail address. StepSecurity assessed that the attacker obtained a long-lived classic npm access token to publish directly to the registry, bypassing GitHub Actions CI/CD controls.
Supply chain security firm Socket identified two additional packages distributing the same malware: @shadanai/openclaw across four versions and @qqbrowser/openclaw-qbot version 0.0.130. The latter ships a tampered copy of the malicious Axios 1.14.1 inside its own node_modules directory.
Socket: "The real axios has only three dependencies (follow-redirects, form-data, proxy-from-env). The addition of plain-crypto-js is unambiguous tampering."
The malicious versions and plain-crypto-js have been removed from npm. Users who installed Axios 1.14.1 or 0.30.4 are advised to downgrade to 1.14.0 or 0.30.3, remove plain-crypto-js from their node_modules directory, check for RAT artifacts at the paths specific to their operating system, rotate all credentials on affected systems, and audit CI/CD pipelines for runs that pulled the compromised versions.