Tax season phishing now ships with QR codes, revoked certificates, and a 29,000-user blast radius.
Microsoft Threat Intelligence reports a predictable April surge in tax-themed phishing, but this year the lures hide something sharper: legitimate remote monitoring and management (RMM) tools turned into remote-access trojans.
Between January and March 2026 the company logged multiple campaigns that deliver ScreenConnect, SimpleHelp, or Datto instead of traditional malware, letting attackers piggyback on signed, trusted software to stay inside victim networks.
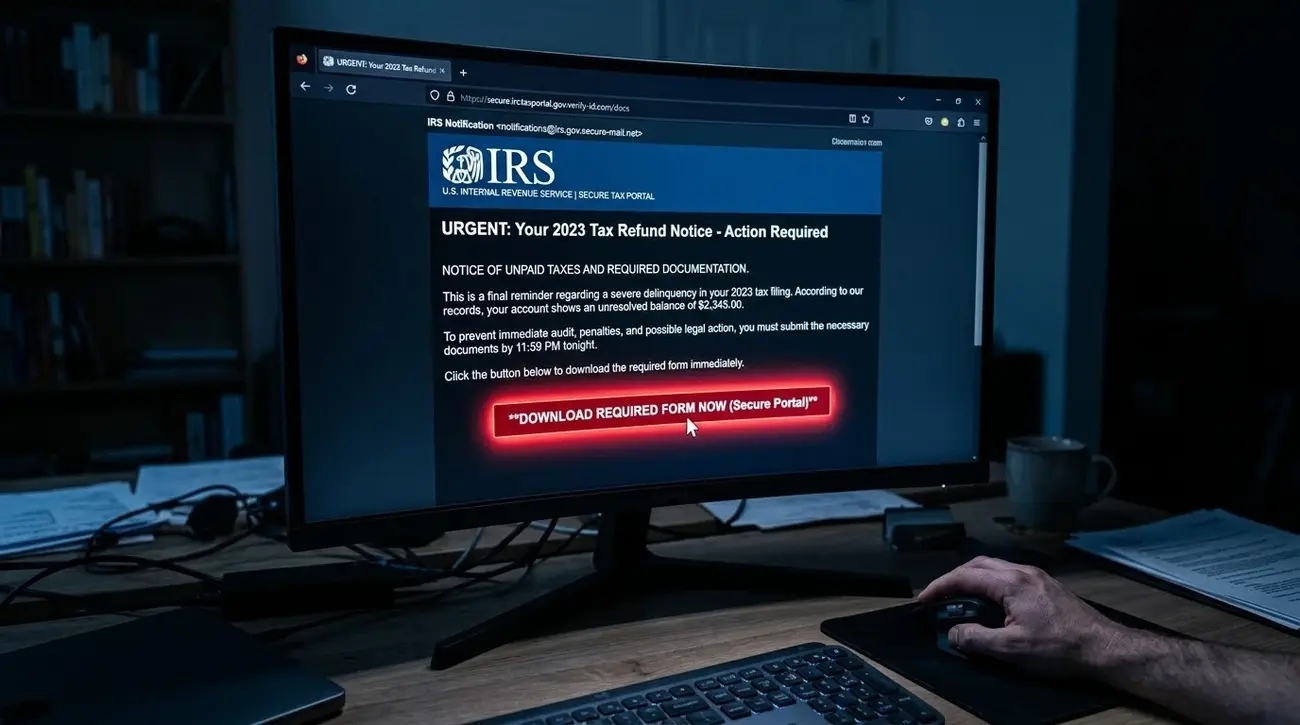
The largest wave hit 29,000 users across 10,000 organizations on February 10. Messages masquerading as "IRS e-File Services" claimed irregular returns had been filed under the recipient's Electronic Filing Identification Number and offered a fake "IRS Transcript Viewer 5.1." The download was simply ScreenConnect—already signed by ConnectWise—repurposed to give attackers hands-on-keyboard control. The same certificate has since been revoked for high abuse.
Earlier in February a Form 1099 campaign used look-alike domains such as taxationstatments2025.com to push the same RMM payload, while a cryptocurrency variant asked targets to copy-paste a non-clickable Eventbrite-sender link that ultimately served either ScreenConnect or SimpleHelp.
A separate Certified Public Accountant (CPA) lure in early February used an Excel attachment named after a real accountant, led victims through OneNote on OneDrive, and landed on the Energy365 phishing kit to harvest credentials.
All campaigns share a common trait: they rely on the victim's trust in tax-time urgency and the perceived legitimacy of the software being installed. Because the RMM tools are genuine, many endpoint defenses allow them to run, giving attackers a persistent remote desktop session without firing a traditional malware signature.
Microsoft recommends enforcing multifactor authentication on every account, enabling zero-hour auto purge in Office 365, and configuring Safe Links to re-check URLs at click time. Defender XDR customers can hunt for the listed SHA-256 hashes and domains using the provided Kusto queries.
Source: Microsoft