Twenty million qubits. That was the barrier. A few years ago, scientists believed quantum computers would need that many to threaten the encryption securing global communications. Two new papers now put the number at 10,000.
The revision arrives from researchers at Caltech and Oratomic, a Pasadena quantum computing company. They calculated that a quantum computer with 9,988 qubits could crack elliptic curve cryptography, the system protecting much of today's internet traffic. The operation would take roughly 1,000 days. With 26,000 qubits, the same encryption falls in a single day.
RSA-2048, another widespread standard, would require 100,000 qubits and 10 days to break. That figure still dwarfs current hardware, but it represents a collapse in scale from previous estimates. The papers were posted March 30 to arXiv.org and have not undergone peer review.
The drop stems from advances in quantum error correction. Quantum bits are fragile; they decohere, lose information, introduce noise. Error correction stitches multiple faulty physical qubits into one reliable logical qubit. The overhead is enormous. Standard schemes demand hundreds or thousands of physical qubits per logical one.
Both research teams employed quantum low-density parity check codes, a more efficient approach. These codes reduce the number of physical qubits needed for each logical qubit. They do impose a cost: each qubit must interact with many others, not just nearest neighbors. That connectivity is hard to achieve on chip-based systems where qubits sit fixed in place.
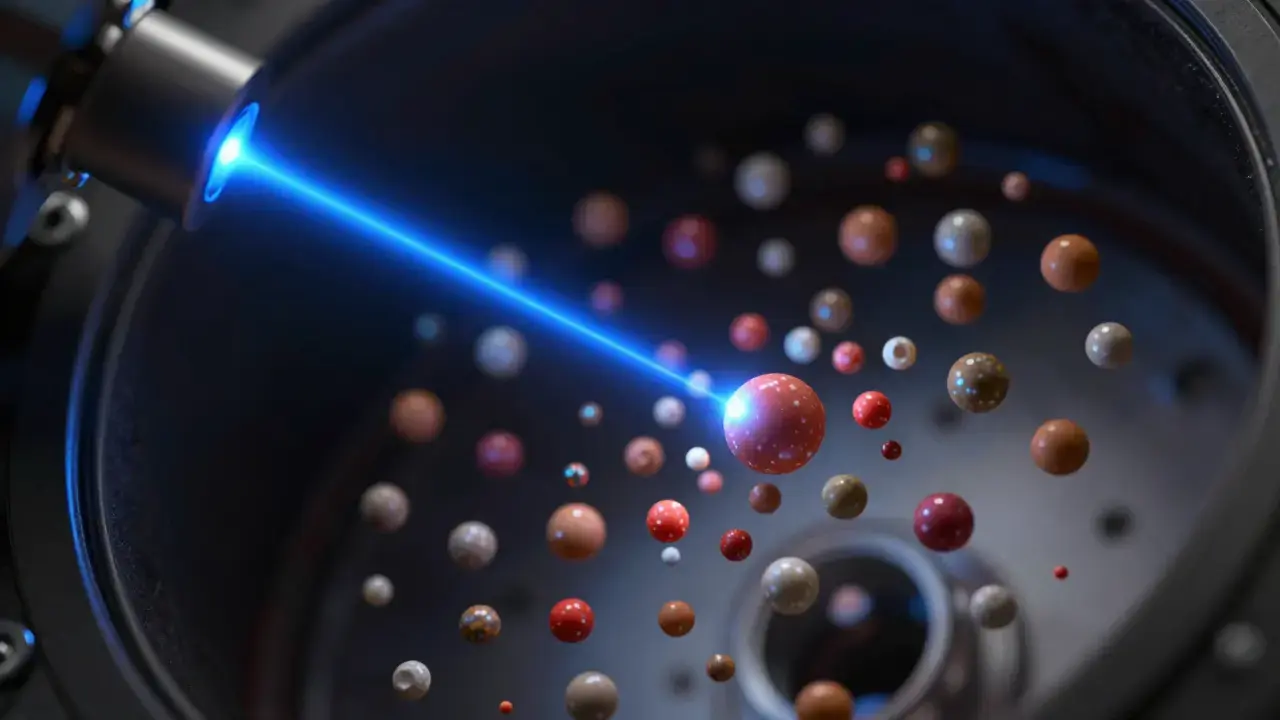
Oratomic's design uses individual atoms as qubits. Lasers reposition them, enabling any-to-any connections. The architecture sidesteps the connectivity problem that constrains other platforms.
Jens Eisert, a physicist at Freie Universität Berlin not involved in the research, sees the result as shifting feasibility itself.
Jens Eisert:
"It has a huge implication on quantum computing. This work is encouraging [in] that it tells us that this may be more feasible than we think."
The implications extend beyond academic interest. Mathematician Jens Niklas Eberhardt of Johannes Gutenberg University Mainz, also uninvolved, describes a "vibe shift" taking hold.
Jens Niklas Eberhardt:
"There's a new wave of hope that quantum computers can really work, and maybe in the next five to 10 years can really crack our encryption. It's kind of amazing but also terrifying."
The terror has specific targets. Bitcoin and other cryptocurrencies rely on elliptic curve cryptography. Their security assumptions rest on the computational difficulty of breaking that encryption. A 10,000-qubit machine does not yet exist. But the path to one no longer looks like a generation-long march.
Google Quantum AI added urgency with its own March 30 announcement. The company suggested that 500,000 physical qubits running for minutes could endanger cryptocurrency security. The figure is larger than Oratomic's estimate but the timeline is compressed to minutes, not days.
Physicist Dolev Bluvstein of Oratomic speaks of error-corrected quantum computing as approaching inevitability.
Dolev Bluvstein:
"It just looks so close and it seems so attainable that there's no way humanity is going to stop."
Scott Aaronson, a computer scientist at the University of Texas at Austin, delivered a more direct message in an email. He called the results "an even stronger impetus for people to upgrade now to quantum-resistant cryptography." His closing instruction: "They should really get on it!"
The papers await peer review. Error correction advances continue arriving rapid-fire. The encryption protecting today's communications was designed to withstand computers that did not exist. The question is no longer whether those computers will arrive. It is whether the defenses will change before they do.
Source: arXiv:2602.11457 | ScienceNews